Technical Writing
Tech Blog
Cloud security, identity, infrastructure, and research. Deep dives, tools, and practical guidance.
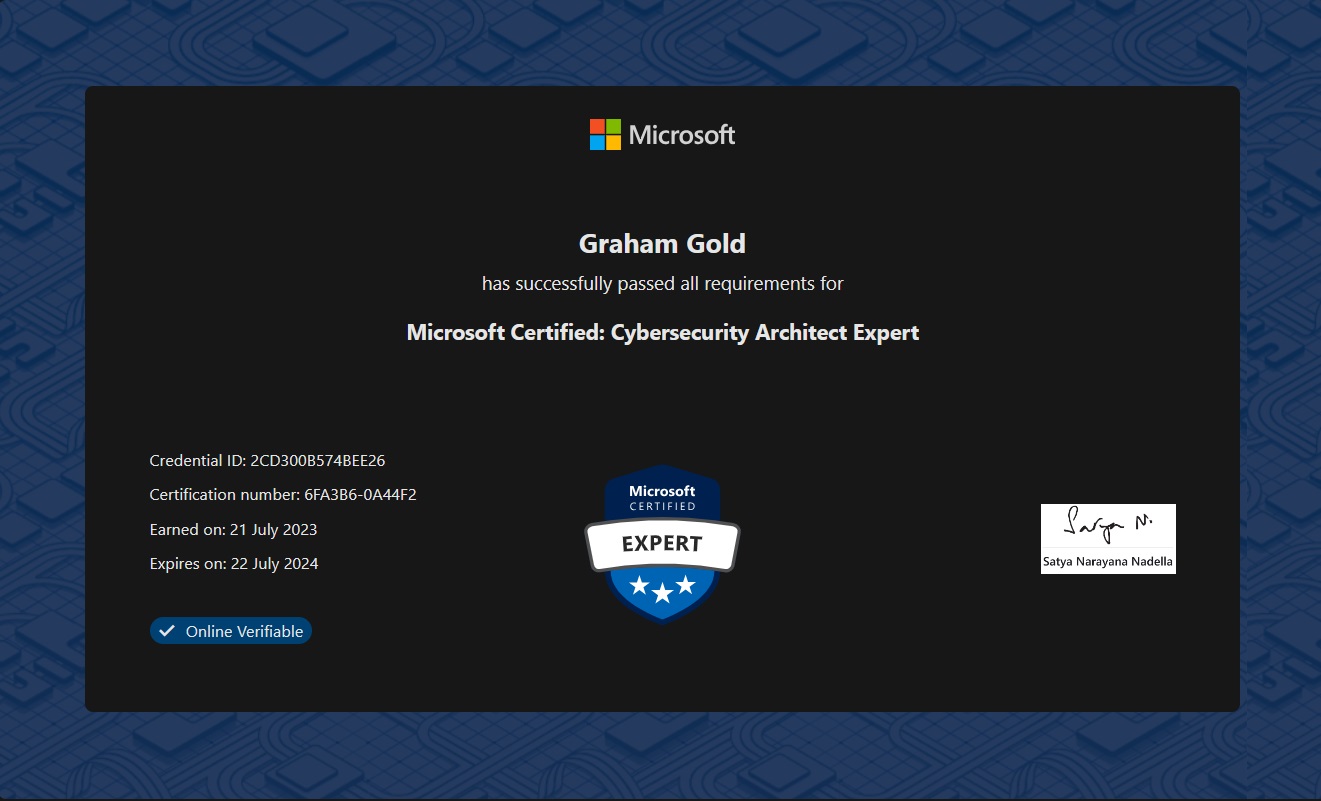
SC-100: Microsoft Certified Cybersecurity Architect
Introduction I recently managed to pass the Microsoft Certified : Cybersecurity Architect (SC-100) exam. In doing so, this, combined with either of SC-300 or AZ-500 (I have both), earned me a new certification - …

My first Microsoft certification renewal experiences - AZ500 and SC300
Exam renewal experiences

How to apply Group Policy tied to an AD Security Group without a reboot
Tips on applying AD Group Policy without rebooting

Introducing: The Audrey Project
Curate your own news!

Keeping up to date with Tech, Cloud and Security info
Introduction In this post, I’m going to talk about something that comes up often enough that its probably worth a post now! I’m often asked how I manage to keep up with whats going in tech in general, and …
Site Structure Changes
This is a very quick update to make you aware of some changes I’ve made: There is a new Personal Blog section for my non-technical blog posts and I have moved my Job Interview and Invisible Illness posts there. …