Technical Writing
Tech Blog
Cloud security, identity, infrastructure, and research. Deep dives, tools, and practical guidance.

How I became a Google Professional Cloud Security Engineer for free and you can too
Want to become a Google Cloud Certified Professional Cloud Security Engineer? Want to do it for free? Read on to find out how!

How Cloud Service Providers Are Failing At Shared Security Responsibility
Introduction In this post, I’m going to talk about a commonly discussed idea that cloud service providers (CSPs) are responsible for managing the risks associated with their services, in partnership with their …
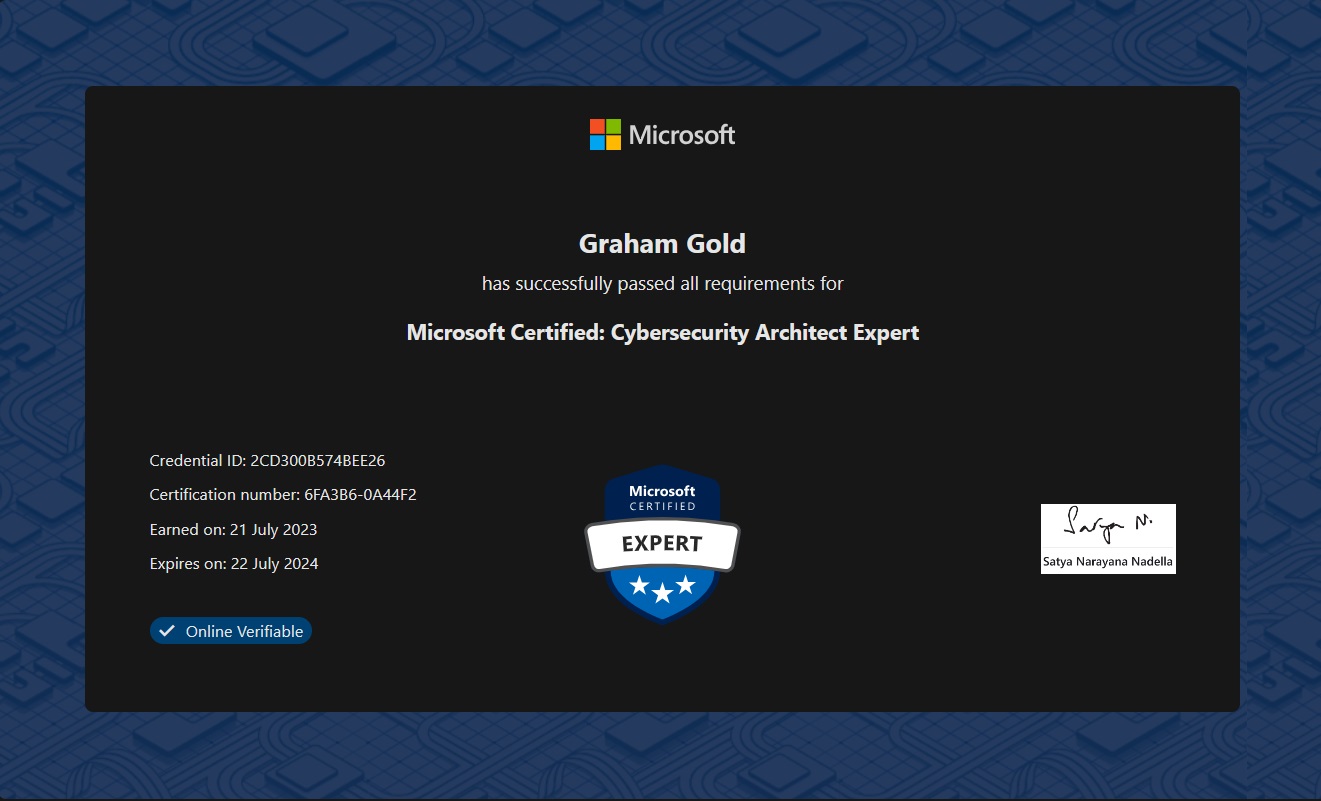
SC-100: Microsoft Certified Cybersecurity Architect
Introduction I recently managed to pass the Microsoft Certified : Cybersecurity Architect (SC-100) exam. In doing so, this, combined with either of SC-300 or AZ-500 (I have both), earned me a new certification - …

My first Microsoft certification renewal experiences - AZ500 and SC300
Exam renewal experiences

How to apply Group Policy tied to an AD Security Group without a reboot
Tips on applying AD Group Policy without rebooting

Introducing: The Audrey Project
Curate your own news!