Technical Writing
Tech Blog
Cloud security, identity, infrastructure, and research. Deep dives, tools, and practical guidance.
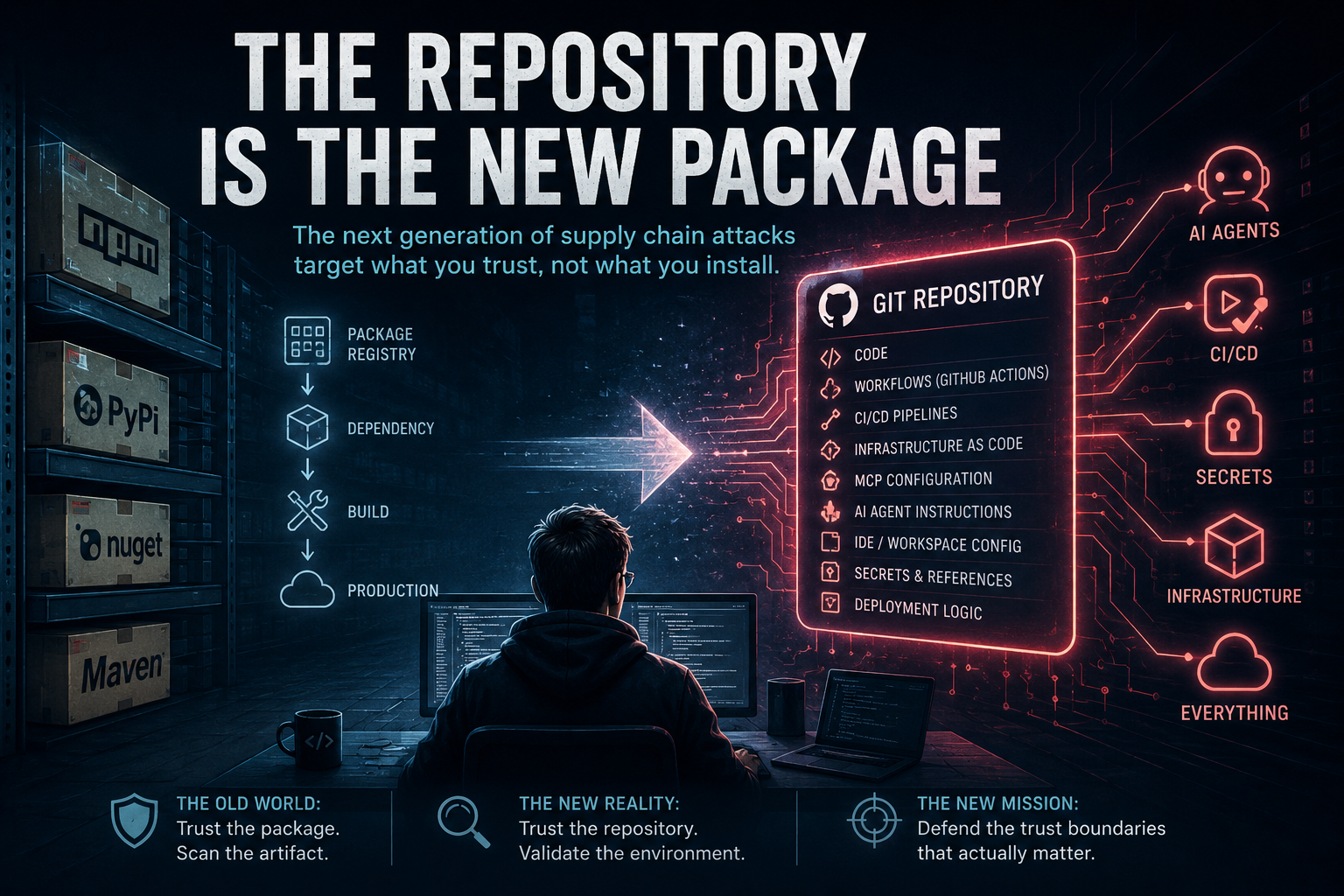
The Repository Is The New Package
The next generation of supply chain attacks aren’t targeting packages. They’re targeting repositories. The June 2026 Azure Functions incident may be a glimpse into what that future looks like.
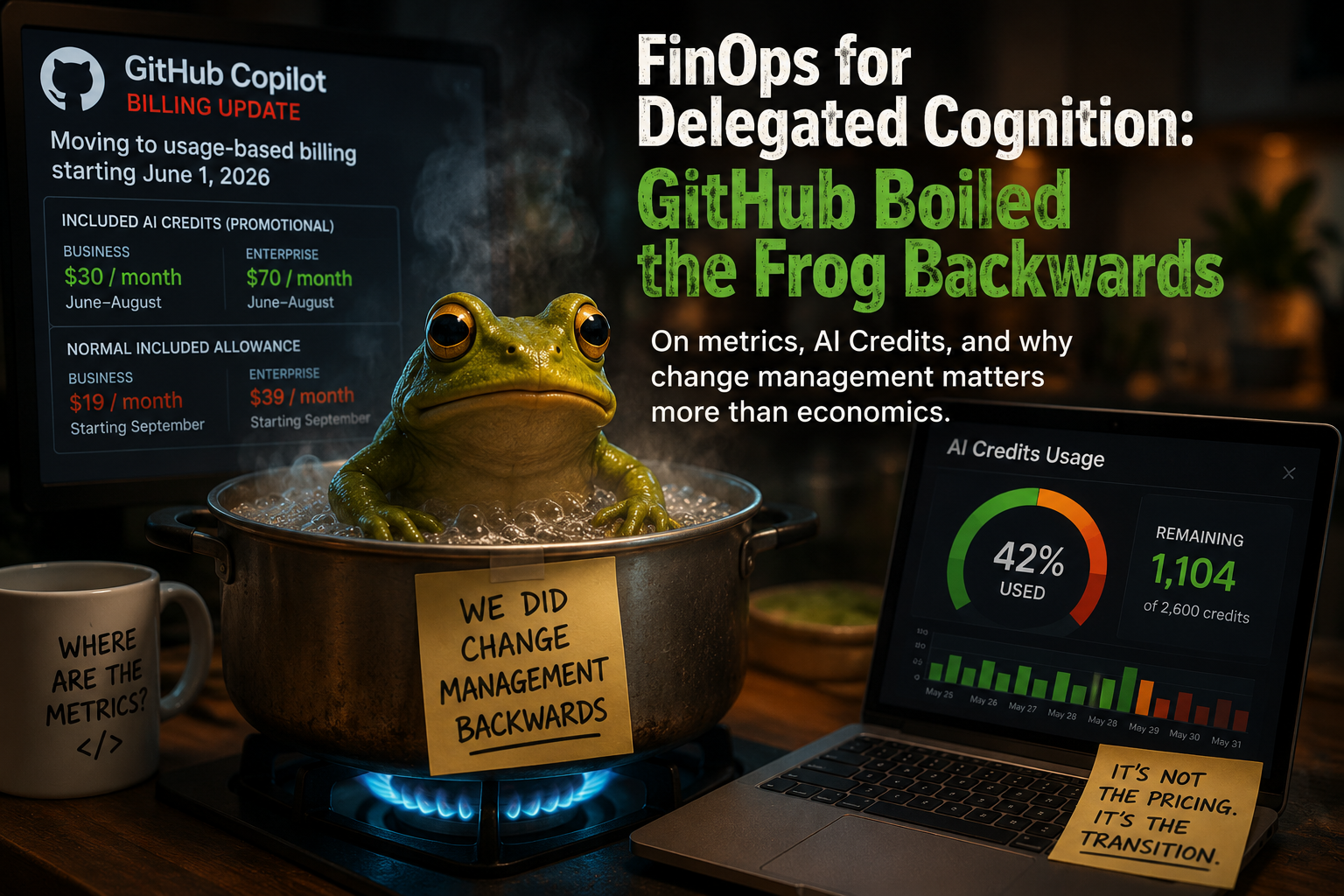
FinOps for Delegated Cognition: GitHub Boiled the Frog Backwards
GitHub's AI Credits rollout wasn't really a pricing story. It was a change-management story, an observability story, and perhaps the first glimpse of FinOps for delegated cognition.

The AI Credits Era Begins: Notes From the First Morning of GitHub’s New Billing Model
First observations from GitHub Copilot’s move from Premium Requests to AI Credits: compatibility fields, confusing reports, missing model attribution, and why AI FinOps now needs its own flight data recorder.
FinOps for Delegated Cognition: AADLCv2 and the Cost of Letting Agents Rediscover Gravity
A follow-up to AADLC: how usage-based AI billing, semantic hydration, prompt-as-code, and field-testing turned a coding workflow into a governance model for delegated cognition.

ISeeMP: What Your AI System Can Actually Be Made To Do
From capabilities to consequences: mapping, testing, and proving exploit paths in MCP-driven AI systems.

Sculpting with Agents: From Prompting to the Agile Agentic Development Life Cycle (AADLC)
How cost pressure, structured baselines, clean context, and multi-model orchestration led to a practical agentic SDLC.